Socket, the biz behind the Wormhole file transfer web app, on Tuesday plans to introduce a security scanning app also called Socket to defend against supply-chain attacks in the JavaScript ecosystem.
For those developing with JavaScript and related technologies, GitHub’s NPM Package Registry is an essential resource. It’s the home of more than 1.8 million packages – libraries and modules that get added to applications as dependencies to perform useful functions.
But its popularity has made it an attractive way to distribute malicious code, because compromised packages can reach a massive audience with minimal effort. WhiteSource, a security firm based in Israel, says that it detected and reported 1,300 malicious npm packages last year.
The Socket application aims to detect supply chain attacks before they do damage. In an email to The Register, Feross Aboukhadijeh, a prolific open-source developer and co-founder/CEO of Socket, explained that attacks on the open-source software supply chain have been getting worse since 2015 and he now sees them nearly every week.
The situation became bad enough, he said, that he felt it was necessary to vet the open source dependencies in Wormhole, a web-based file transfer app promising security through encryption. “I didn’t feel comfortable telling people to trust our service with their most precious data when malware could be lurking in any dependency that we update to a new version,” he explained.
Aboukhadijeh said the standard approach has been to scan for known vulnerabilities, or CVE-labeled flaws. But these kinds of programming blunders take a long time to discover and for public reports to appear, and finding and fixing these types of bugs is not on the same level as identifying deliberately compromised dependencies.
The 200-day gap
Pointing to a 2020 research paper [PDF] that found malware typically lurks in hosted packages for 200 days before being detected, Aboukhadijeh said it was clear that bad packages had to be caught before they got integrated into developers’ apps.
For Wormhole, that meant auditing every open-source package in the app.
“Fortunately, most supply chain attacks follow a similar pattern (stealing environment variables, sending data to the network, etc.) so we built a tool that would have caught all of the recent NPM supply chain attacks,” explained Aboukhadijeh. “The tool analyzes the actual behavior of the package instead of relying on stale data in a CVE database.”
There are already a great many vulnerability scanning and static analysis tools available. But according to Aboukhadijeh, these fail to stop the supply-chain attacks on NPM that we’ve seen – ua-parser-js, coa, rc, colors, faker, event-stream, eslint-scope, and so on.
“Traditional vulnerability scanning tools merely look up the package versions you’re using and compare them to public CVE data in the National Vulnerability Database,” Aboukhadijeh said. “When they find a match, they send you an alert to upgrade to a new version.
Traditional static analysis tools are way too noisy when run on third-party code, and don’t provide actionable results. Socket, on the other hand, is intended to provide meaningful advice.
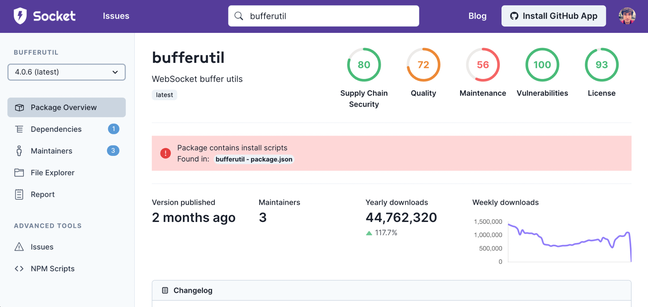
The app looks for malware, typo-squatting, hidden/obfuscated/minified code, the introduction of risky APIs (filesystem, network, child_process, eval()), and suspicious updates. It currently supports 70 detections across five categories: supply chain risk, quality, maintenance, known vulnerabilities, and license problems.
“Socket uses static analysis (and soon, dynamic analysis) to characterize the behavior of a package and determine what capabilities it uses, which we call ‘capability detection,'” said Aboukhadijeh. “For instance, to determine if an npm package uses the network, Socket looks at whether `fetch()`, or Node’s `net`, `dgram`, `dns`, or `http` or `https` modules are used within the package or – and this part is key – any of its dependencies. We also look for redundant signals, such as the presence URL or IP address fragments in strings.
The app also looks at what’s going on outside the code in analyzed packages, to detect, for example, efforts to quietly acquire a popular package and then subvert it.
“Some of the most valuable security signals come from side channels such as maintainer behavior,” said Aboukhadijeh. “Socket detects ‘unstable ownership‘ which is when a new maintainer is given publish permission on a package. We also detect when packages are published out of chronological order because attackers often publish new patches on old major versions which still have a lot of usage.”
It also looks for typo-squatting, which involves submitting a package to NPM that’s named in a way that’s confusingly similar to another package, in the hope of tricking developers into installing the malicious version.
Really opening up security
Aboukhadijeh said those testing the app have already caught multiple instances of malware that they’ve reported and NPM has removed.
“Beyond outright malware, Socket users have discovered an interesting new open source trend: some maintainers have started including telemetry in their packages to gather runtime usage statistics,” said Aboukhadijeh. “This is similar to how websites include trackers such as Google Analytics. We have already added a detection in Socket for this issue so companies can detect and block telemetry from their open source. We’re keeping an eye on this trend.”
Aboukhadijeh said his company wants to open up Socket’s tools to security researchers who are looking for NPM malware and said those interested should get in touch.

Malicious backdoored NPM package masqueraded as Twilio library for three days until it was turfed out
Socket is currently available as an integrated GitHub app – clicking the install button from the Socket website takes you to a GitHub permission prompt. Once authorized, it runs with each pull request, evaluating changes to package manifest files such as package.json. When a new dependency gets added, Socket will evaluate it and leave a comment if it’s a security risk, said Aboukhadijeh.
There’s a Socket CLI and API in the pipeline. And the service is free for public repos, a benefit also available to private repos for a limited time. Socket package search and package health scores are available at no cost from the company’s website. Socket integrations, such as the GitHub app, are free for open source repositories, “forever” we’re told. For private repos, the service is free while beta testing is going on. Pricing for private repos after general availability has yet to be decided.
“In the coming weeks, we’ll ship a new detection for packages with maintainers who use email addresses with expired domains, which is a huge risk factor for package hijacking,” Aboukhadijeh said. “We’re also working on new signals such as maintainer reputation, maintainer burnout, and maintainer security practices (2FA enabled, code signing, security policy posted).”
“Our goal is for Socket to provide the most comprehensive open source risk analysis on the market, and that means analyzing the full picture – from maintainers and how they behave, to open-source codebases and how they evolve.” ®